Our Services
Enterprise-Level Asset Protection for Your Bottom Line.
At High Keep Asset Protection, we understand that shrinkage is rarely just a "cost of doing business"—it is a symptom of operational vulnerabilities. We bring the rigorous, data-driven security standards used in the world's largest logistics networks directly to your operation.
Whether you are bleeding inventory, experiencing unexplained cash shortages, or simply need to harden your physical facility, we provide targeted, measurable solutions.

Data-Driven Shrink & Transaction Analysis
Uncovering the hidden leaks in your daily operations.
Modern theft and loss often hide in the data before they are ever caught on camera. We conduct deep-dive audits of your financial and inventory metrics to pinpoint exactly where your margins are eroding.
Point-of-Sale (POS) Exception Reporting: We analyze transaction logs for high-risk activity, including excessive voids, zero-dollar transactions, manual discounts, and suspicious returns.
Inventory Reconciliation: Identifying the specific gap between your expected stock and actual on-hand inventory, isolating whether the loss is occurring at the receiving dock, the sales floor, or the register.
Cash Shortage Tracing: Methodical breakdown of daily cash logs, drawer openings, and shift changes to identify anomalies and recover missing funds.
Custom SOP Development & Team Training
Building a culture of proactive loss prevention.
The best security system in the world is an educated, vigilant staff. We don't just leave you with a report; we equip your team to maintain a secure environment.
Standard Operating Procedure (SOP) Drafting: Custom-written, easy-to-follow security and operational guidelines tailored specifically to your business model.
Staff Awareness Training: On-site workshops teaching your employees how to safely spot shoplifters, identify internal red flags, and handle emergency security situations.
Leadership Coaching: Training your management team on how to enforce asset protection standards and maintain accountability on every shift.
Facility Hardening & Physical Security Assessments
Transforming your location into a hard target.
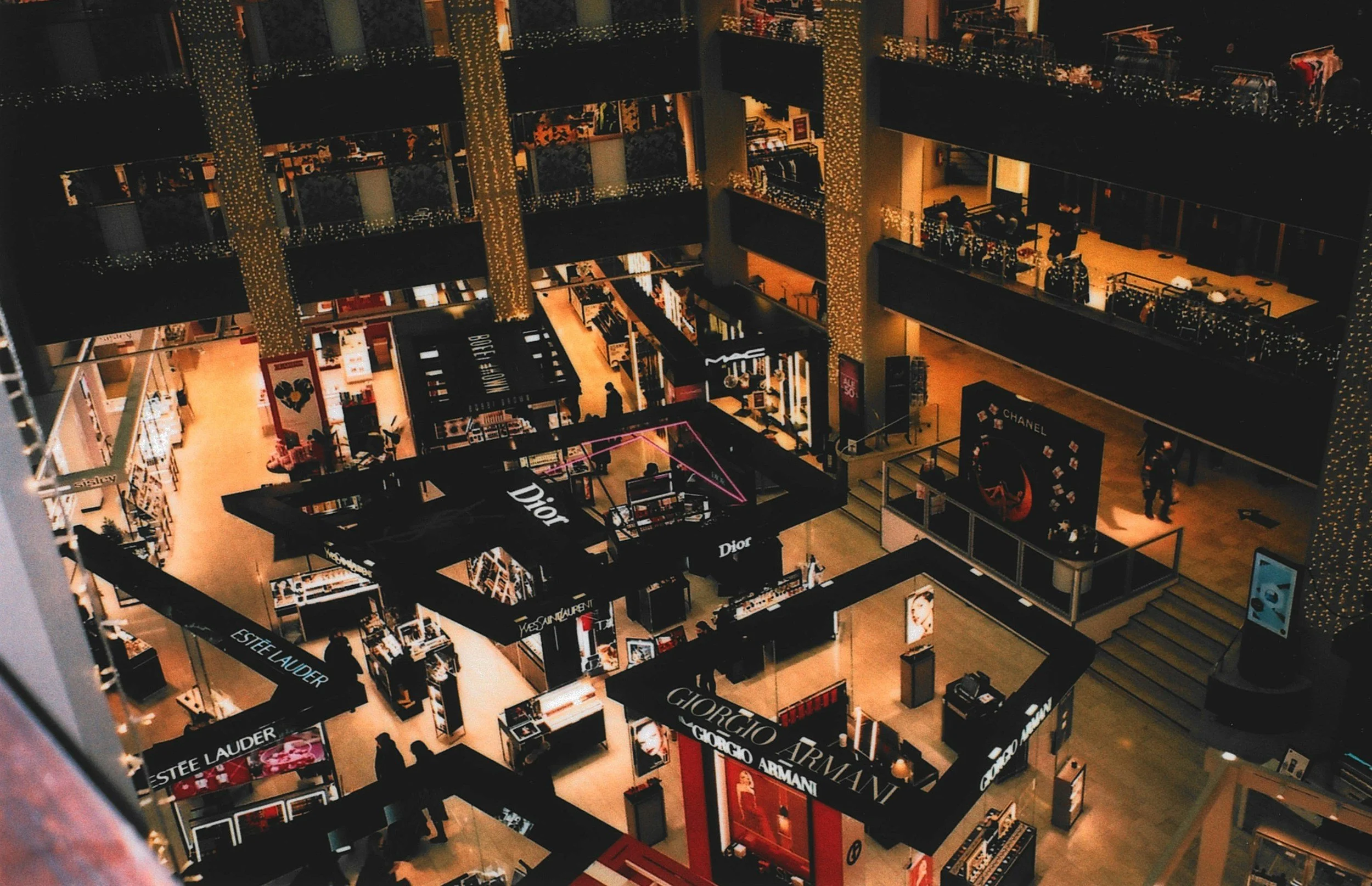
A secure perimeter and a well-designed interior are your first lines of defense. We conduct comprehensive, on-site evaluations of your physical footprint to eliminate blind spots and deter both external and internal threats.
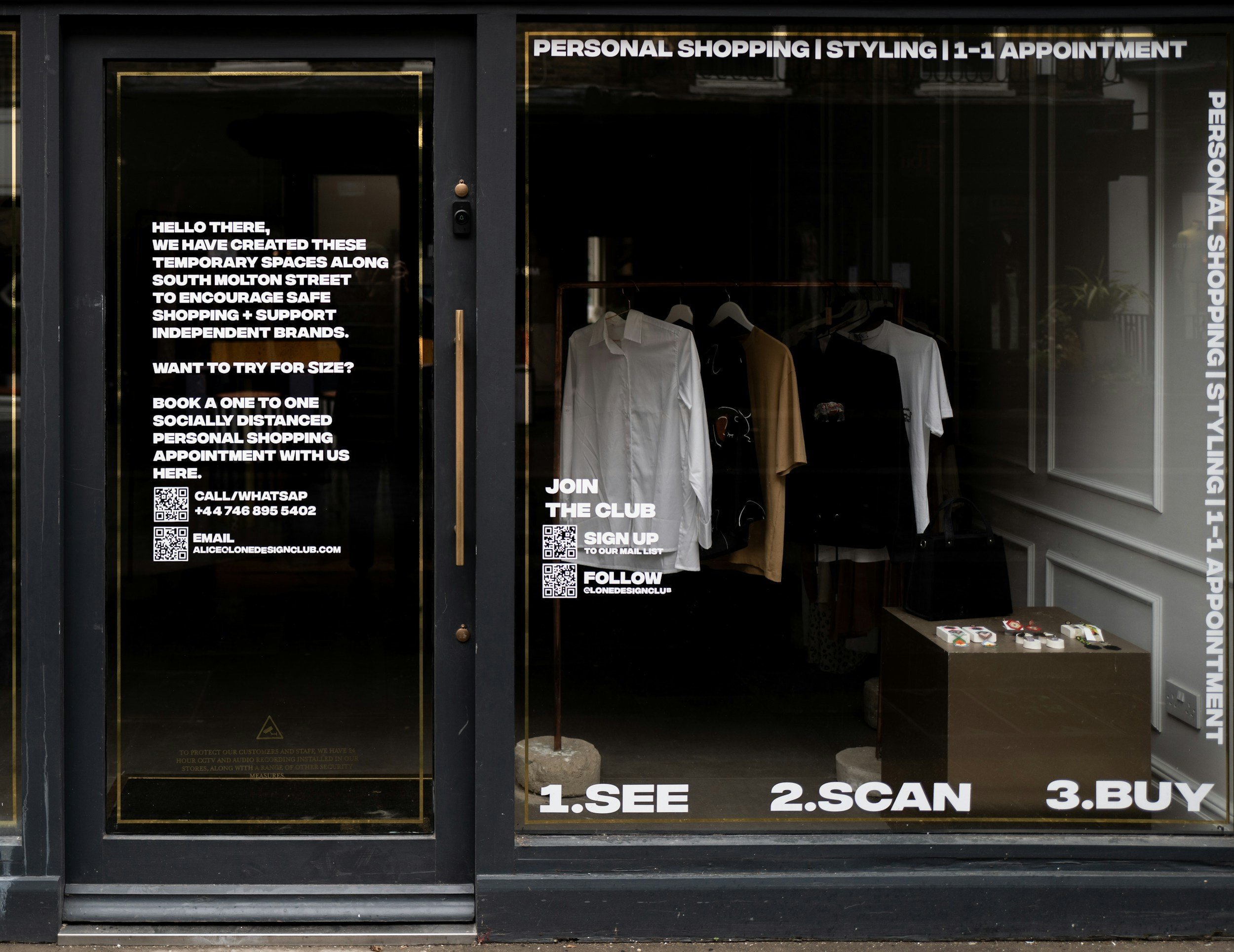
CCTV & Surveillance Optimization: Evaluating camera placement, resolution needs, and field-of-view to ensure critical areas (registers, safes, receiving doors, high-value merchandise) are constantly monitored.
Access Control Audits: Reviewing key management, alarm code distribution, and restricted-area protocols to ensure only authorized personnel have access to your most sensitive assets.
Merchandise Protection Strategies: Implementing practical, high-visibility deterrents for high-theft items without negatively impacting the customer shopping experience.

Operational Compliance & Workflow Audits
Closing the procedural gaps that cause accidental and intentional loss.
Vulnerabilities often exist within standard daily routines. We map your operations from the back door to the front counter to ensure your processes are secure.
Supply Chain & Receiving Audits: Ensuring vendor deliveries are properly verified, logged, and secured before they ever hit the floor.
Opening & Closing Procedures: Reviewing the critical moments of your business day to ensure cash handling and building security are locked down.
Trash & Waste Control: A common avenue for internal theft. We audit how waste and damaged goods are processed and removed from the building.
Internal Investigations & Resolution
Discreet, professional handling of suspected internal theft or fraud.
When you suspect an employee or a vendor is stealing, acting without evidence or a clear strategy can create legal liability. We provide the expertise to handle these situations cleanly.
Evidence Compilation & Case Building: We discreetly gather the necessary data, video, and paper trails required to prove theft or fraud definitively.
Strategic Interviewing: Structuring the conversation to obtain admissions, recover stolen assets, and ensure a smooth termination process.
Post-Incident Mitigation: Once an issue is resolved, we immediately implement the structural fixes needed to ensure that specific type of theft cannot happen again.
Contact us
Interested in working together? Fill out some info and we will be in touch shortly. We can’t wait to hear from you!
